In this article, we will provide a brief overview of Silverfort’s platform, the first (and currently only) unified identity protection platform on the market. Silverfort’s patented technology aims to protect organizations from identity-based attacks by integrating with existing identity and access management solutions, such as AD (Active Directory) and cloud-based services, and extending secure access controls like Risk-Based Authentication and MFA (Multi-Factor Authentication) to all their resources. This includes on-prem and cloud resources, legacy systems, command-line tools and service accounts.
A recent report by Silverfort and Osterman Research revealed that 83% of organizations worldwide have experienced data breaches due to compromised credentials. Many organizations admit that they are underprotected against identity-based attacks, such as lateral movement and ransomware. Resources like command-line access tools and legacy systems, which are widely used, are particularly challenging to protect.
Getting Started: Using the Dashboard
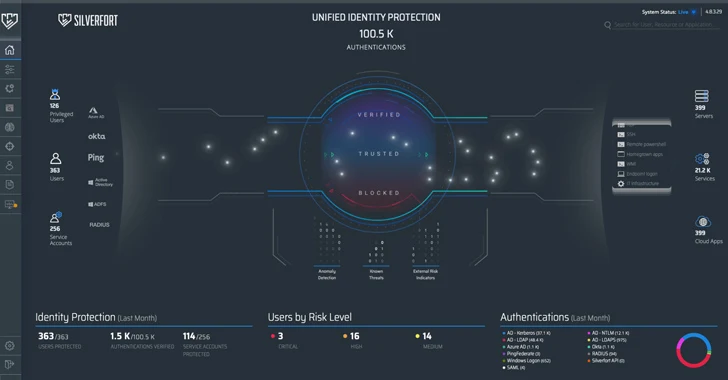
Below is a screenshot of Silverfort’s dashboard (figure 1). Overall, it has a very intuitive user interface. On the left is a list of user types: privileged users, standard users, and service accounts, and how they access resources: through on-prem and cloud-based directories (AD, Azure AD, Okta), federation servers (Ping, ADFS), and VPN connections (RADIUS). The right side of the screen displays a list of the different resource types users attempt to access. The access attempts are represented by glowing dots.
This display showcases the platform’s unique differentiator – it’s the only solution today that’s capable of integrating with the entire identity infrastructure in the hybrid environment. With this integration in place, the different on-prem and cloud directories forward every authentication and access attempt to Silverfort for analysis and verdict whether to allow access or deny. In that manner, real time protection for any user and resource is achieved, as we’ll soon see in more detail.
The dashboard also shows aggregations of valuable identity-related data: number of authentication attempts by protocols and directories, proportion of verified authentications, number of users and service accounts successfully protected, and a breakdown of users by risk level (medium, high, critical).
The platform includes various modules with each one addressing a different identity protection issue. We’ll now explore two of them: Advanced MFA and Service Account Protection.
Protecting Resources with Advanced MFA
MFA has proven to be one of the most effective ways to protect against identity-based attacks. However, having MFA protection on all network assets is pretty hard.
MFA traditionally relies on agents and proxies, which means some computers will never be covered by it. Either because your network is too large to have proxies on every single computer, or because not all computers are capable of installing agents.
Want to see Silverfort in action? Schedule a free demo with our team of experts today!
Moreover, command-line access tools, such as PsExec, PowerShell, and WMI, despite being widely used by network admins, do not natively support MFA. These and other on-prem authentications are managed by AD, but AD authentication protocols (Kerberos, NTLM) were simply not designed for MFA, and attackers know that. AD only checks whether usernames and passwords match, so attackers using legitimate credentials (which may or may not be compromised) can access the network and launch lateral movement and ransomware attacks without AD knowing. Silverfort’s major advantage is that it can actually enforce MFA on all of these, something other solutions can’t.
On the policy screen (figure 2) you can view existing policies or create new ones.
| Figure 2: Policy screen |
Creating a new policy seems pretty intuitive, as seen in figure 3. We need to determine the authentication type, the relevant protocols, what users, sources, and destinations the policy covers, and the action required. What happens here is actually pretty simple, but surprisingly clever. AD sends all authentication and access requests to Silverfort. For each request, Silverfort analyzes its risk and associated policies to determine whether MFA is required or not. Depending on the verdict, the user is granted access, blocked, or requested to provide MFA. In other words, the policy basically bypasses the inherent limitations of older protocols and enforces MFA on them.
| Figure 3: Creating a policy |
Discovering and Securing Service Accounts
Service accounts are a critical security challenge due to their high access privileges and low to zero visibility. Moreover, service accounts aren’t humans, so MFA isn’t an option, and so is password rotation with PAM, which may crash critical processes if their logins fail. In fact, all organizations have multiple service accounts, sometimes as many as 50% of their overall users, and many of them go unmonitored. That’s why attackers love compromised service accounts- they can use them for lateral movement under the radar and gain access to a large number of machines without being noticed.
Figure 4 shows the Service Accounts screen. As Silverfort receives all authentication and access requests, it is able to identify service accounts by analyzing repetitive machine behaviors.
| Figure 4: Service Accounts screen |
It looks like we have 162 accounts under machine-to-machine. We can filter them based on a variety of parameters. Predictability, for example, measures repeated access to the same source or destination. Deviations from this pattern can indicate malicious activity.
In figure 5, we can see additional information about our service accounts, such as sources, destinations, risk indicators, privilege levels, and usage.
| Figure 5: Service account Investigation screen |
For each service account, policies are automatically created based on its behavior. All we have to do is choose between ‘alert’, ‘block’ and ‘alert to SIEM’, and enable the policy (figure 6).
| Figure 6: Service account policies |
Final Thoughts
Silverfort’s platform truly achieves its goal of unified identity protection. Its ability to enforce MFA on practically any resource (such as command-line tools, legacy apps, file shares, and many others) and create policies in seconds is unparalleled. Having full visibility into all service accounts and finally being able to protect them is extremely valuable. To conclude, Silverfort’s platform offers innovative identity protection capabilities that are becoming increasingly necessary each day.










