The advanced persistent threat (APT) actor known as SideWinder has been accused of deploying a backdoor in attacks directed against Pakistan government organizations as part of a campaign that commenced in late November 2022.
“In this campaign, the SideWinder advanced persistent threat (APT) group used a server-based polymorphism technique to deliver the next stage payload,” the BlackBerry Research and Intelligence Team said in a technical report published Monday.
Another campaign discovered by the Canadian cybersecurity company in early March 2023 shows that Turkey has also landed in the crosshairs of the threat actor’s collection priorities.
SideWinder has been on the radar since at least 2012 and it’s primarily known to target various Southeast Asian entities located in Pakistan, Afghanistan, Bhutan, China, Myanmar, Nepal, and Sri Lanka.
Suspected to be an Indian state-sponsored group, SideWinder is also tracked under the monikers APT-C-17, APT-Q-39, Hardcore Nationalist (HN2), Rattlesnake, Razor Tiger, and T-APT4.
Typical attack sequences mounted by the actor entail using carefully crafted email lures and DLL side-loading techniques to fly under the radar and deploy malware capable of granting the actors remote access to the targeted systems.
Over the past year, SideWinder has been linked to a cyber attack aimed at Pakistan Navy War College (PNWC) as well as an Android malware campaign that leveraged rogue phone cleaner and VPN apps uploaded to the Google Play Store to harvest sensitive information.
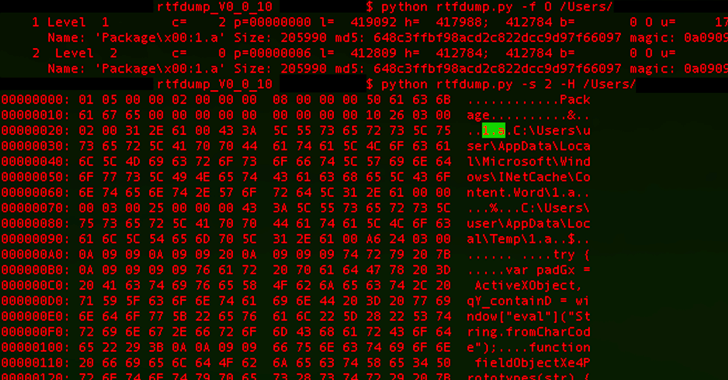
The latest infection chain documented by BlackBerry mirrors findings from Chinese cybersecurity firm QiAnXin in December 2022 detailing the use of PNWC lure documents to drop a lightweight .NET-based backdoor (App.dll) that’s capable of retrieving and executing next-stage malware from a remote server.
What makes the campaign also stand out is the threat actor’s use of server-based polymorphism as a way to potentially sidestep traditional signature-based antivirus (AV) detection and distribute additional payloads by responding with two different versions of an intermediate RTF file.
Specifically, the PNWC document employs a method known as remote template injection to fetch the RTF file such that it harbors the malicious code only if the request originates from a user in the Pakistan IP address range.
“It is important to note that in both instances, only the name of the file ‘file.rtf’ and the file type are the same; however, the contents, file size and the file hash are different,” BlackBerry explained.
Learn to Stop Ransomware with Real-Time Protection
Join our webinar and learn how to stop ransomware attacks in their tracks with real-time MFA and service account protection.
“If the user is not in the Pakistani IP range, the server returns an 8-byte RTF file (file.rtf) that contains a single string: {rtf1 }. However, if the user is within the Pakistani IP range, the server then returns the RTF payload, which varies between 406 KB – 414 KB in size.”
The disclosure arrives shortly after Fortinet and Team Cymru disclosed details of attacks perpetrated by a Pakistan-based threat actor known as SideCopy against Indian defense and military targets.
“The latest SideWinder campaign targeting Turkey overlaps with the most recent developments in geopolitics; specifically, in Turkey’s support of Pakistan and the ensuing reaction from India,” BlackBerry said.






