Cybersecurity researchers have discovered a new information stealer dubbed SYS01stealer targeting critical government infrastructure employees, manufacturing companies, and other sectors.
“The threat actors behind the campaign are targeting Facebook business accounts by using Google ads and fake Facebook profiles that promote things like games, adult content, and cracked software, etc. to lure victims into downloading a malicious file,” Morphisec said in a report shared with The Hacker News.
“The attack is designed to steal sensitive information, including login data, cookies, and Facebook ad and business account information.”
The Israeli cybersecurity company said the campaign was initially tied to a financially motivated cybercriminal operation dubbed Ducktail by Zscaler.
However, WithSecure, which first documented the Ducktail activity cluster in July 2022, said the two intrusion sets are different from one another, indicating how the threat actors managed to confuse attribution efforts and evade detection.
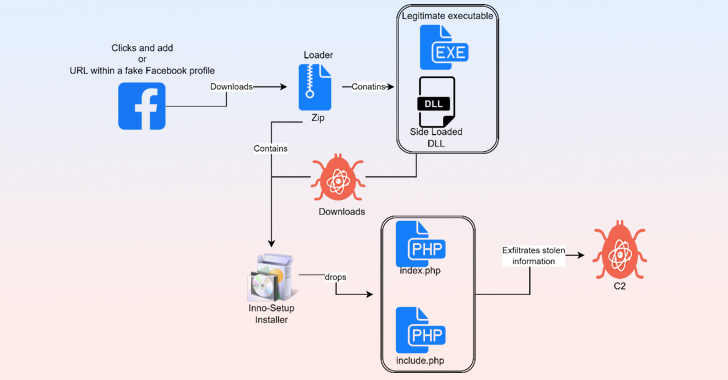
The attack chain, per Morphisec, commences when a victim is successfully lured into clicking on a URL from a fake Facebook profile or advertisement to download a ZIP archive that purports to be cracked software or adult-themed content.
Opening the ZIP file launches a based loader – typically a legitimate C# application – that’s vulnerable to DLL side-loading, thereby making it possible to load a malicious dynamic link library (DLL) file alongside the app.
Some of the applications abused to side-load the rogue DLL are Western Digital’s WDSyncService.exe and Garmin’s ElevatedInstaller.exe. In some instances, the side-loaded DLL acts as a means to deploy Python and Rust-based intermediate executables.
Irrespective of the approach employed, all roads lead to the delivery of an installer that drops and executes the PHP-based SYS01stealer malware.
The stealer is engineered to harvest Facebook cookies from Chromium-based web browsers (e.g., Google Chrome, Microsoft Edge, Brave, Opera, and Vivaldi), exfiltrate the victim’s Facebook information to a remote server, and download and run arbitrary files.
Discover the Latest Malware Evasion Tactics and Prevention Strategies
Ready to bust the 9 most dangerous myths about file-based attacks? Join our upcoming webinar and become a hero in the fight against patient zero infections and zero-day security events!
It’s also equipped to upload files from the infected host to the command-and-control (C2) server, run commands sent by the server, and update itself when a new version is available.
The development comes as Bitdefender revealed a similar stealer campaign known as S1deload that’s designed to hijack users’ Facebook and YouTube accounts and leverage the compromised systems to mine cryptocurrency.
“DLL side-loading is a highly effective technique for tricking Windows systems into loading malicious code,” Morphisec said.
“When an application loads in memory and search order is not enforced, the application loads the malicious file instead of the legitimate one, allowing threat actors to hijack legitimate, trusted, and even signed applications to load and execute malicious payloads.”








