Cybersecurity researchers have warned of a new malicious Python package that has been discovered in the Python Package Index (PyPI) repository to facilitate cryptocurrency theft as part of a broader campaign.
The package in question is pytoileur, which has been downloaded 316 times as of writing. Interestingly, the package author, who goes by the name PhilipsPY, has uploaded a new version of the package (1.0.2) with identical functionality after a previous version (1.0.1) was yanked by PyPI maintainers on May 28, 2024.
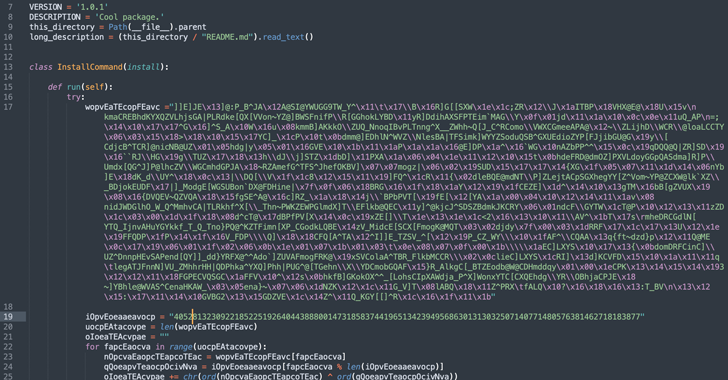
According to an analysis released by Sonatype, the malicious code is embedded in the package’s setup.py script, allowing it to execute a Base64-encoded payload that’s responsible for retrieving a Windows binary from an external server.
“The retrieved binary, ‘Runtime.exe,’ is then run by leveraging Windows PowerShell and VBScript commands on the system,” security researcher Ax Sharma said.
Once installed, the binary establishes persistence and drops additional payloads, including spyware and a stealer malware capable of gathering data from web browsers and cryptocurrency services.
Sonatype said it also identified a newly created StackOverflow account called “EstAYA G” responding to users’ queries on the question-and-answer platform, directing them to install the rogue pytoileur package as a supposed solution to their issues.
“While definitive attribution is challenging when assessing pseudonymous user accounts on internet platforms without access to logs, the recent age of both of these user accounts and their sole purpose of publishing and promoting the malicious Python package gives us a good indication that these are linked to the same threat actor(s) behind this campaign,” Sharma told The Hacker News.
The development marks a new escalation in that it abuses a credible platform as a propagation vector for malware.
“The unprecedented open abuse of such a credible platform, using it as a breeding ground for malicious campaigns, is a huge warning sign for developers globally,” Sonatype further said in a statement shared with The Hacker News.
“StackOverflow’s compromise is especially concerning given the large number of novice developers it has, who are still learning, asking questions, and may fall for malicious advice.”
A closer examination of the package metadata and its authorship history has revealed overlaps with a prior campaign involving bogus Python packages such as Pystob and Pywool, which was disclosed by Checkmarx in November 2023.
The findings are another example of why open-source ecosystems continue to be a magnet for threat actors looking to compromise several targets all at once with information stealers like Bladeroid and other malware by means of what’s called a supply chain attack.








