A never-before-seen complex malware is targeting business-grade routers to covertly spy on victims in Latin America, Europe, and North America at least since July 2022.
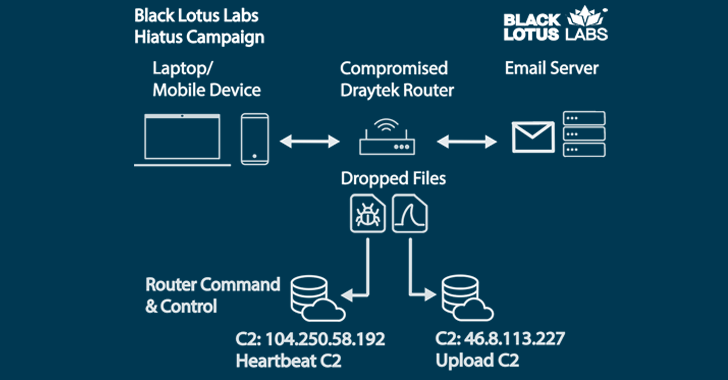
The elusive campaign, dubbed Hiatus by Lumen Black Lotus Labs, has been found to deploy two malicious binaries, a remote access trojan dubbed HiatusRAT and a variant of tcpdump that makes it possible to capture packet capture on the target device.
“Once a targeted system is infected, HiatusRAT allows the threat actor to remotely interact with the system, and it utilizes prebuilt functionality […] to convert the compromised machine into a covert proxy for the threat actor,” the company said in a report shared with The Hacker News.
“The packet-capture binary enables the actor to monitor router traffic on ports associated with email and file-transfer communications.”
The threat cluster primarily singles out end-of-life (EoL) DrayTek Vigor router models 2960 and 3900, with approximately 100 internet-exposed devices compromised as of mid-February 2023. Some of the impacted industry verticals include pharmaceuticals, IT services/consulting firms, and municipal government, among others.
Interestingly, this represents only a small fraction of the 4,100 DrayTek 2960 and 3900 routers that are publicly accessible over the internet, raising the possibility that “the threat actor is intentionally maintaining a minimal footprint to limit their exposure.”
Given that the impacted devices are high-bandwidth routers that can simultaneously support hundreds of VPN connections, it’s being suspected that the goal is to spy on targets and establish a stealthy proxy network.
“These devices typically live outside the traditional security perimeter, which means they usually are not monitored or updated,” Mark Dehus, director of threat intelligence for Lumen Black Lotus Labs, said. “This helps the actor establish and maintain long-term persistence without detection.”
The exact initial access vector used in the attacks is unknown, but a successful breach is followed by the deployment of a bash script that downloads and executes HiatusRAT and a packet-capture binary.
HiatusRAT is feature-rich and can harvest router information, running processes, and contact a remote server to fetch files or run arbitrary commands. It’s also capable of proxying command-and-control (C2) traffic through the router.
Discover the Latest Malware Evasion Tactics and Prevention Strategies
Ready to bust the 9 most dangerous myths about file-based attacks? Join our upcoming webinar and become a hero in the fight against patient zero infections and zero-day security events!
The use of compromised routers as proxy infrastructure is likely an attempt to obfuscate the C2 operations, the researchers said.
The findings come more than six months after Lumen Black Lotus Labs also shed light on an unrelated router-focused malware campaign that used a novel trojan called ZuoRAT.
“The discovery of Hiatus confirms that actors are continuing to pursue router exploitation,” Dehus said. “These campaigns demonstrate the need to secure the router ecosystem, and routers should be regularly monitored, rebooted, and updated, while end-of-life devices should be replaced.”




