It’s been a year since the release of The Ultimate SaaS Security Posture Management (SSPM) Checklist. If SSPM is on your radar, here’s the 2023 checklist edition, which covers the critical features and capabilities when evaluating a solution.
The ease with which SaaS apps can be deployed and adopted today is remarkable, but it has become a double-edged sword. On the one hand, apps are quickly onboarded, employees can work from anywhere, and there is little need for operational management. On the other hand, there are pain points that stem from the explosion of SaaS app usage, explained by the “3 V” s:
- Volume: Each app can have hundreds of global settings. Multiply this number by thousands – or tens (or even hundreds) of thousands – of employees. Security teams must first be able to discover all the users who are using each application, as well as familiarize themselves with every application’s specific set of rules and configurations, and ensure they are compliant with their company’s policies.
- Visibility: With this incredibly high volume of configurations, user roles and permissions, devices and SaaS-to-SaaS access, security teams need multi-dimensional visibility to monitor them all, identify when there is an issue, and remediate it swiftly.
- Velocity: The speed of change that SaaS apps bring are incredibly hard to govern. SaaS apps are dynamicand ever-evolving — apps’ settings need to be modified on a continuous basis from security updates and app feature enhancements to employees added or removed, and user roles and permissions set, reset, updated, etc. There are also continuous, compliance updates to meet industry standards and best practices (NIST, SOC2, ISO, MITRE, etc.) that need to be checked and modified.
Named by Gartner as a MUST HAVE solution in the “4 Must-Have Technologies That Made the Gartner Hype Cycle for Cloud Security, 2021,” SaaS Security Posture Management (SSPM) solutions come to answer these pains to provide full visibility and gain control of the company’s SaaS security posture.
As one might expect, not all SSPM solutions are created equal. The Misconfiguration Management use case sits at the core of SSPM. However, there are more advanced use cases that tackle the emerging and growing challenges existing in the SaaS landscape.
- Misconfiguration Management: Deep visibility and control of all configurations, settings, and built-in security controls across all SaaS apps for all users
- SaaS-to-SaaS App Access: Monitoring and management of all third-party apps connected to the company’s core SaaS stack
- Identity & Access Management Governance: Consolidation and validation of User Identity and Access, enabling attack surface reduction, efficient SecOps programs, and operational integrity (for example, identifying dormant accounts or external users with administrative access)
- Device-to-SaaS User Risk Management: Manage risks stemming for the SaaS user’s device based on the device hygiene score
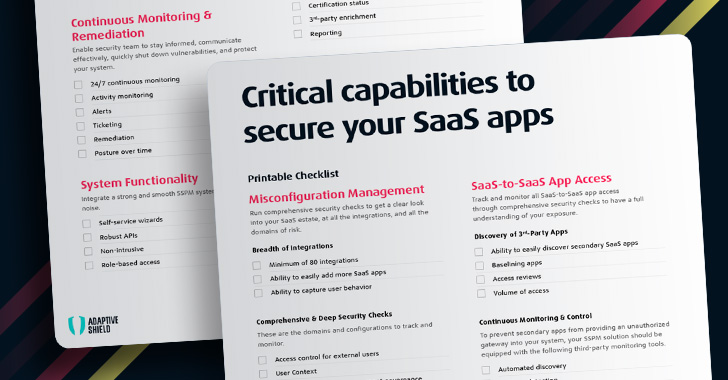
When comparing SSPM options, here are some key features and capabilities to look out for (excerpted from the complete guide):
Misconfiguration Visibility & Insights
Run comprehensive security checks to get a clear look into your SaaS estate, at all the integrations, and all the domains of risk.
Breadth
First and foremost for an SSPM’s core solution, is the SSPM’s ability to integrate with all your SaaS apps.
- Look for an SSPM system that will integrate with any application and is able to run checks on every data type to protect against misconfigurations.
- Each SaaS has its own framework and configurations; if there is access to users and the company’s systems, it should be monitored by the organization. Any app can pose a risk, even non-business-critical apps. Your SSPM should allow you to easily add more apps.
- Point of note is that users are the key to managing many of your misconfigurations. Look for an SSPM that has the capability to capture user behavior.
Comprehensive & Deep Security Checks
The other vital component to a core SSPM solution is the expanse and depth of the security checks. Each domain has its own facets for the security team to track and monitor.
- Access control for external users
- User Context
- Identity and access management governance
- Malware protection
- Data leakage protection
- Auditing
- Privacy control
- Compliance policies, security frameworks and benchmarks
Get the complete guide along with the printable checklist here.
Continuous Monitoring & Remediation
Combat threats with continuous oversight and fast remediation of any misconfiguration
Remediating issues in business environments is a complicated and delicate task. The core SSPM solution should provide deep context about each and every configuration and enable you to easily monitor and set up alerts. This way vulnerabilities are quickly closed before they are exploited by cyberattacks.
SSPM vendors like Adaptive Shield provide you with these tools, which allow your security team to communicate effectively, shut down vulnerabilities, and protect your system.
- 24/7 continuous monitoring
- Activity monitoring
- Alerts
- Ticketing
- Remediation
- Posture over time
System Functionality
Your SSPM solution should be easy to deploy and allow your security team to easily add and monitor new SaaS applications. Top security solutions should integrate easily with your applications and your existing cybersecurity infrastructure, to create a comprehensive defense against cyber threats.
- Self-service wizards
- Robust APIs
- Non-intrusive
- Role-based access
SaaS-to-SaaS App Access Visibility & Insights
In an effort to improve productivity, employees often extend the functionality of their primary SaaS applications by connecting them to a secondary SaaS app, or otherwise known as 3rd-party app access. These rights include the ability to read, create, update, and delete corporate or personal data. This access is granted in seconds, usually far outside the view of the IT and security teams, and significantly increases an organization’s attack surface.
However, users rarely realize they’ve handed over significant permission rights to the new 3rd-party application. These 3rd-party applications, which can number in the thousands for larger organizations, all must be monitored and overseen by the security team.
To prevent secondary apps from providing an unauthorized gateway into your system, your SSPM solution should be equipped with the following capabilities:
- Ability to easily discover 3rd-party SaaS apps
- Access Reviews
- Volume of Access
- Settings Detection
- Consolidate API Clients
- Scope Breakdowns
- Identification
- Create Standardized System
- User Context
- Installation Dates
- Certification Status
- 3rd-Party Enrichment
- Reporting
Device-to-SaaS User Risk Visibility & Insights
Even before employees were routinely working from home, user devices posed a risk to corporate networks. Security teams had no visibility into the owners of different devices and couldn’t ensure that the devices were secure. When individuals with advanced privilege levels use devices that are unsecured, they expand the attack surface with what amounts to an open gateway.
Track and monitor all device-to-SaaS user risk to eliminate surprise vulnerabilities
Associating Devices with Users
- User Information
- Risk Scoring
- Device Discoverability
- Reporting
- Device Posture Data
- Operating System Verification
- Device to User Correlation
- Device Posture Data
Identity & Access Management Visibility & Insights
Over time, the number of users with access to different parts of an enterprise’s system increases. While some users may move on, oftentimes they remain in the system and retain the same privileges that they had. Threat actors or disgruntled associates of the company can use these credentials to gain access to unauthorized areas of the system. Security teams need a tool to identify and disconnect these users from multiple environments and applications within the company. They also need to monitor every SaaS login and ensure that user activity meets security guidelines.
Identify all users with access to any system or application within the environment:
User Authorizations
- SSO
- MFA
- Password Management
- Authentication Protocols
- Video Conferencing
Identifying Users
- User Discovery
- User Classification
- Guest Status
- Privileged Users
- Full Employee Visibility
- User Risk Level
- Platform Context
- Dormant Accounts
- Administrative Permissions
- Reporting
- Unique Permission Identification
- Oversight
- Unauthorized Users
Final Thoughts
The Right SSPM solution PREVENTS your next attack.
SSPM is similar to brushing one’s teeth: it’s a foundational requirement needed to create a preventative state of protection. The right SSPM provides organizations continuous, automated surveillance of all SaaS apps, alongside a built-in knowledge base to ensure the highest SaaS security hygiene.
Learn more about how you can secure your company’s SaaS security now.




