admin
October 6, 2023
Ensuring sensitive data remains confidential, protected from unauthorized access, and compliant with data privacy regulations is paramount....
admin
October 6, 2023
GitHub has announced an improvement to its secret scanning feature that extends validity checks to popular services such as...
admin
October 6, 2023
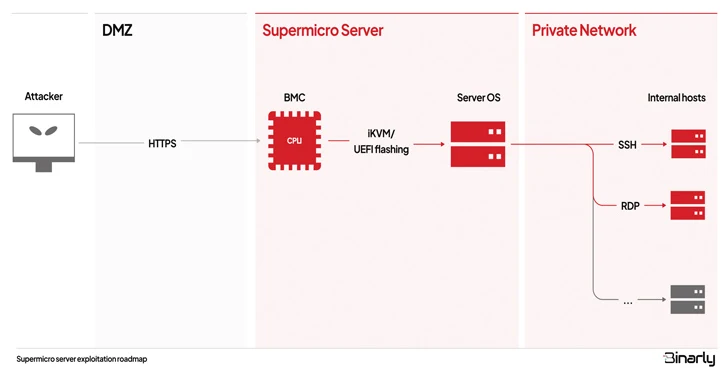
Multiple security vulnerabilities have been disclosed in the Intelligent Platform Management Interface (IPMI) firmware for Supermicro baseboard...
QakBot Threat Actors Still in Action, Using Ransom Knight and Remcos RAT in Latest Attacks


2 min read
admin
October 5, 2023
Despite the disruption to its infrastructure, the threat actors behind the QakBot malware have been linked to...
admin
October 5, 2023
Cisco has released updates to address a critical security flaw impacting Emergency Responder that allows unauthenticated, remote...
Analysis and Config Extraction of Lu0Bot, a Node.js Malware with Considerable Capabilities


5 min read
admin
October 5, 2023
Nowadays, more malware developers are using unconventional programming languages to bypass advanced detection systems. The Node.js malware...
admin
October 5, 2023
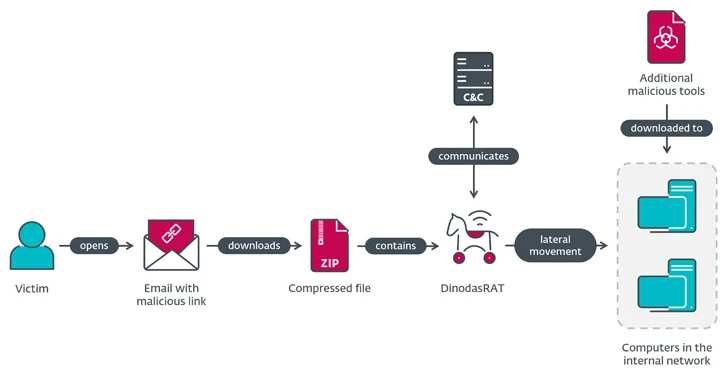
A governmental entity in Guyana has been targeted as part of a cyber espionage campaign dubbed Operation Jacana.
The activity,...
admin
October 5, 2023
A new Android banking trojan named GoldDigger has been found targeting several financial applications with an aim...
admin
October 5, 2023
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added two security flaws to its Known Exploited Vulnerabilities...
admin
October 5, 2023
Apple on Wednesday rolled out security patches to address a new zero-day flaw in iOS and iPadOS...
admin
October 5, 2023
Atlassian has released fixes to contain an actively exploited critical zero-day flaw impacting publicly accessible Confluence Data...
admin
October 4, 2023
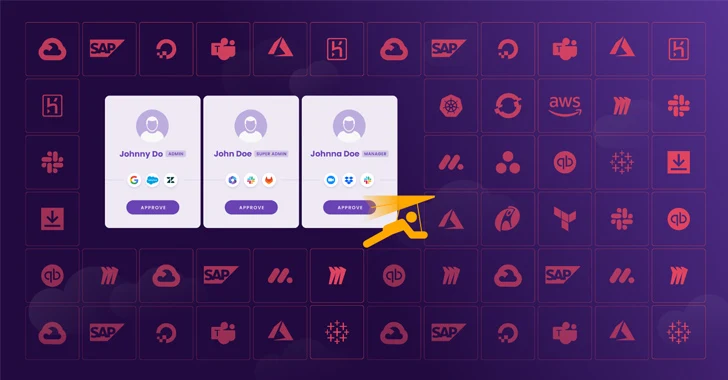
Today, mid-sized companies and their CISOs are struggling to handle the growing threat of SaaS security with...
admin
October 4, 2023
A new deceptive package hidden within the npm package registry has been uncovered deploying an open-source rootkit...
admin
October 4, 2023
New findings have identified connections between an Android spyware called DragonEgg and another sophisticated modular iOS surveillanceware...
admin
October 4, 2023
Microsoft has detailed a new campaign in which attackers unsuccessfully attempted to move laterally to a cloud...
admin
October 4, 2023
A new Linux security vulnerability dubbed Looney Tunables has been discovered in the GNU C library's ld.so...
admin
October 3, 2023
APIs, also known as application programming interfaces, serve as the backbone of modern software applications, enabling seamless...
admin
October 3, 2023
Security Configuration Assessment (SCA) is critical to an organization's cybersecurity strategy. SCA aims to discover vulnerabilities and misconfigurations...
admin
October 3, 2023
Chipmaker Qualcomm has released security updates to address 17 vulnerabilities in various components, while warning that three...
admin
October 3, 2023
Cybersecurity researchers have disclosed multiple critical security flaws in the TorchServe tool for serving and scaling PyTorch models that...