The P2PInfect peer-to-peer (P2) worm has been observed employing previously undocumented initial access methods to breach susceptible Redis servers and rope them into a botnet.
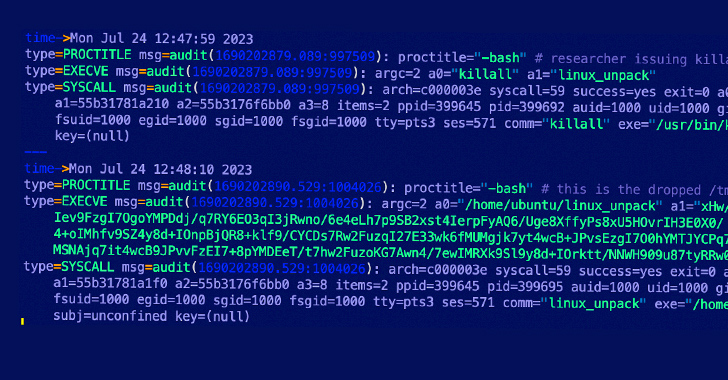
“The malware compromises exposed instances of the Redis data store by exploiting the replication feature,” Cado Security researchers Nate Bill and Matt Muir said in a report shared with The Hacker News.
“A common attack pattern against Redis in cloud environments is to exploit this feature using a malicious instance to enable replication. This is achieved via connecting to an exposed Redis instance and issuing the SLAVEOF command.”
The Rust-based malware was first documented by Palo Alto Networks Unit 42, calling out the malware’s ability to exploit a critical Lua sandbox escape vulnerability (CVE-2022-0543, CVSS score: 10.0) to obtain a foothold into Redis instances. The campaign is believed to have commenced on or after June 29, 2023.
However, the latest discovery suggests that the threat actors behind the campaign are leveraging multiple exploits for initial access.
This is not the first time the SLAVEOF command has been abused in the wild. Previously, threat actors associated with malware families such as H2Miner and HeadCrab have abused the attack technique to illicitly mine cryptocurrency on compromised hosts.
In doing so, the goal is to replicate a malicious instance and load a malicious module to activate the infection.
Another initial access vector entails the registration of a malicious cron job on the Redis host to download the malware from a remote server upon execution, a method previously observed in attacks mounted by the WatchDog cryptojacking group.
A successful breach is followed by the distribution of next-stage payloads that allow the malware to alter iptables firewall rules at will, upgrade itself, and potentially deploy cryptocurrency miners at a later date once the botnet has grown to a specific size.
Shield Against Insider Threats: Master SaaS Security Posture Management
Worried about insider threats? We’ve got you covered! Join this webinar to explore practical strategies and the secrets of proactive security with SaaS Security Posture Management.
“The P2Pinfect malware makes use of a peer-to-peer botnet,” the researchers said. “Each infected server is treated as a node, which then connects to other infected servers. This allows the entire botnet to gossip with each other without using a centralized C2 server.”
A notable trait of the botnet is its worming behavior, enabling it to expand its reach by using a list of passwords to brute-force SSH servers and attempting to exploit the Lua sandbox escape vulnerability or use the SLAVEOF command in the case of Redis servers.
“P2Pinfect is well-designed and utilizes sophisticated techniques for replication and C2,” the researchers concluded. “The choice of using Rust also allows for easier portability of code across platforms (with the Windows and Linux binaries sharing a lot of the same code), while also making static analysis of the code significantly harder.”





