The financially motivated threat actor known as FIN8 has been observed using a “revamped” version of a backdoor called Sardonic to deliver the BlackCat ransomware.
According to the Symantec Threat Hunter Team, part of Broadcom, the development is an attempt on the part of the e-crime group to diversify its focus and maximize profits from infected entities. The intrusion attempt took place in December 2022.
FIN8 is being tracked by the cybersecurity company under the name Syssphinx. Known to be active since at least 2016, the adversary was originally attributed to attacks targeting point-of-sale (PoS) systems using malware such as PUNCHTRACK and BADHATCH.
The group resurfaced after more than a year in March 2021 with an updated version of BADHATCH, following it up with a completely new bespoke implant called Sardonic, which was disclosed by Bitdefender in August 2021.
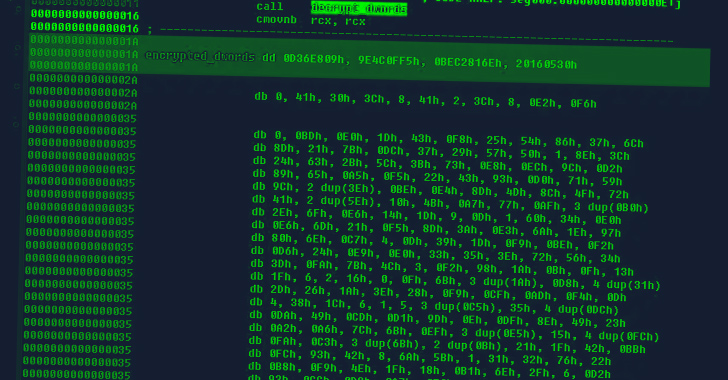
“The C++-based Sardonic backdoor has the ability to harvest system information and execute commands, and has a plugin system designed to load and execute additional malware payloads delivered as DLLs,” Symantec said in a report shared with The Hacker News.
Unlike the previous variant, which was designed in C++, the latest iteration packs in significant alterations, with most of the source code rewritten in C and modified so as to deliberately avoid similarities.
In the incident analyzed by Symantec, Sardonic is embedded into a PowerShell script that was deployed into the targeted system after obtaining initial access. The script is designed to launch a .NET loader, which then decrypts and executes an injector module to ultimately run the implant.
“The purpose of the injector is to start the backdoor in a newly created WmiPrvSE.exe process,” Symantec explained. “When creating the WmiPrvSE.exe process, the injector attempts to start it in session-0 (best effort) using a token stolen from the lsass.exe process.”
Sardonic, besides supporting up to 10 interactive sessions on the infected host for the threat actor to run malicious commands, supports three different plugin formats to execute additional DLL and shellcode.
Shield Against Insider Threats: Master SaaS Security Posture Management
Worried about insider threats? We’ve got you covered! Join this webinar to explore practical strategies and the secrets of proactive security with SaaS Security Posture Management.
Some of the other features of the backdoor include the ability to drop arbitrary files and exfiltrate file contents from the compromised machine to an actor-controlled infrastructure.
This is not the first time FIN8 has been detected using Sardonic in connection with a ransomware attack. In January 2022, Lodestone and Trend Micro uncovered FIN8’s use of the White Rabbit ransomware, which, in itself, is based on Sardonic.
“Syssphinx continues to develop and improve its capabilities and malware delivery infrastructure, periodically refining its tools and tactics to avoid detection,” Symantec said.
“The group’s decision to expand from point-of-sale attacks to the deployment of ransomware demonstrates the threat actors’ dedication to maximizing profits from victim organizations.”









