Multiple threat actors are weaponizing a design flaw in Foxit PDF Reader to deliver a variety of malware such as Agent Tesla, AsyncRAT, DCRat, NanoCore RAT, NjRAT, Pony, Remcos RAT, and XWorm.
“This exploit triggers security warnings that could deceive unsuspecting users into executing harmful commands,” Check Point said in a technical report. “This exploit has been used by multiple threat actors, from e-crime to espionage.”
It’s worth noting that Adobe Acrobat Reader – which is more prevalent in sandboxes or antivirus solutions – is not susceptible to this specific exploit, thus contributing to the campaign’s low detection rate.
The issue stems from the fact that the application shows “OK” as the default selected option in a pop-up when users are asked to trust the document prior to enabling certain features to avoid potential security risks.
Once a user clicks OK, they are displayed a second pop-up warning that the file is about to execute additional commands with the option “Open” set as the default. The command triggered is then used to download and execute a malicious payload hosted on Discord’s content delivery network (CDN).
“If there were any chance the targeted user would read the first message, the second would be ‘Agreed’ without reading,” security researcher Antonis Terefos said.
“This is the case that the Threat Actors are taking advantage of this flawed logic and common human behavior, which provides as the default choice the most ‘harmful’ one.”
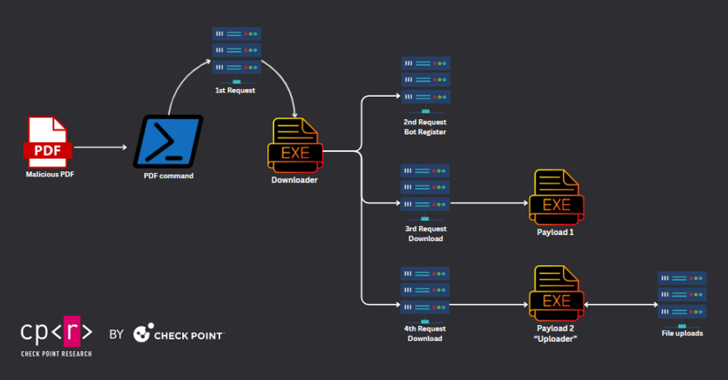
Check Point said it identified a PDF document bearing a military theme that, when opened via Foxit PDF Reader, executed a command to fetch a downloader that, in turn, retrieved two executables to collect and upload data, including documents, images, archive files, and databases to a command-and-control (C2) server.
Further analysis of the attack chain has revealed that the downloader could also be used to drop a third payload that’s capable of capturing screenshots of the infected host, after which they are uploaded to the C2 server.
The activity, assessed to be geared towards espionage, has been linked to DoNot Team (aka APT-C-35 and Origami Elephant), citing overlaps with previously observed tactics and techniques associated with the threat actor.
A second instance weaponizing the same technique employs a multi-stage sequence to deploy a stealer and two cryptocurrency miner modules such as XMRig and lolMiner. Interestingly, some of the booby-trapped PDF files are distributed via Facebook.
The Python-based stealer malware is equipped to steal victims’ credentials and cookies from Chrome and Edge browsers, with the miners retrieved from a Gitlab repository belonging to a user named topworld20241. The repository, created on February 17, 2024, is still active as of writing.
In another case documented by the cybersecurity company, the PDF file acts as a conduit to retrieve from Discord CDN Blank-Grabber, an open-source information stealer that’s available on GitHub and which has been archived as of August 6, 2023.
“Another interesting case occurred when a malicious PDF included a hyperlink to an attachment hosted on trello[.]com,” Terefos said. “Upon downloading, it revealed a secondary PDF file containing malicious code, which takes advantage of this ‘exploitation’ of Foxit Reader users.”
The infection pathway culminates in the delivery of Remcos RAT, but only after progressing through a series of steps that involve the use of LNK files, HTML Application (HTA), and Visual Basic scripts as intermediate steps.
The threat actor behind the Remcos RAT campaign, who goes by the name silentkillertv and claims to be an ethical hacker with over 22 years of experience, has been observed advertising several malicious tools via a dedicated Telegram channel called silent_tools, including crypters and PDF exploits targeting Foxit PDF Reader. The channel was created on April 21, 2022.
Check Point said it also identified .NET- and Python-based PDF builder services such as Avict Softwares I Exploit PDF, PDF Exploit Builder 2023, and FuckCrypt that were used to create the malware-laced PDF files. The DoNot Team is said to have used a .NET PDF builder freely available on GitHub.
If anything, the use of Discord, Gitlab, and Trello demonstrates the continued abuse of legitimate websites by threat actors to blend in with normal network traffic, evade detection, and distribute malware. Foxit has acknowledged the issue and is expected to roll out a fix in version 2024 3. The current version is 2024.2.1.25153.
“While this ‘exploit’ doesn’t fit the classical definition of triggering malicious activities, it could be more accurately categorized as a form of ‘phishing’ or manipulation aimed at Foxit PDF Reader users, coaxing them into habitually clicking ‘OK’ without understanding the potential risks involved,” Terefos said.
“The infection success and the low detection rate allow PDFs to be distributed via many untraditional ways, such as Facebook, without being stopped by any detection rules.”







