It comes as no surprise that today’s cyber threats are orders of magnitude more complex than those of the past. And the ever-evolving tactics that attackers use demand the adoption of better, more holistic and consolidated ways to meet this non-stop challenge. Security teams constantly look for ways to reduce risk while improving security posture, but many approaches offer piecemeal solutions – zeroing in on one particular element of the evolving threat landscape challenge – missing the forest for the trees.
In the last few years, Exposure Management has become known as a comprehensive way of reigning in the chaos, giving organizations a true fighting chance to reduce risk and improve posture. In this article I’ll cover what Exposure Management is, how it stacks up against some alternative approaches and why building an Exposure Management program should be on your 2024 to-do list.
What is Exposure Management?
Exposure Management is the systematic identification, evaluation, and remediation of security weaknesses across your entire digital footprint. This goes beyond just software vulnerabilities (CVEs), encompassing misconfigurations, overly permissive identities and other credential-based issues, and much more.
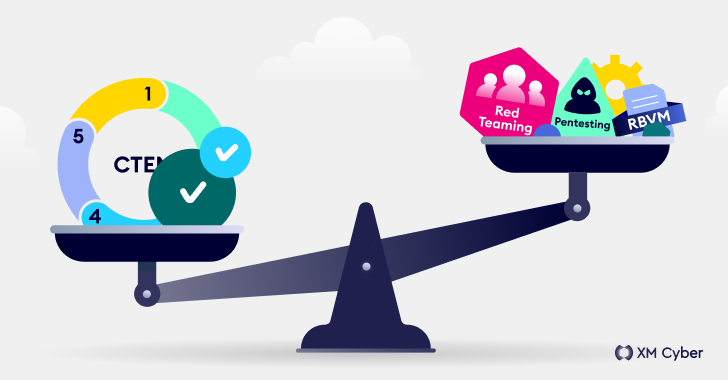
Organizations increasingly leverage Exposure Management to strengthen cybersecurity posture continuously and proactively. This approach offers a unique perspective because it considers not just vulnerabilities, but how attackers could actually exploit each weakness. And you may have heard of Gartner’s Continuous Threat Exposure Management (CTEM) which essentially takes Exposure Management and puts it into an actionable framework. Exposure Management, as part of CTEM, helps organizations take measurable actions to detect and prevent potential exposures on a consistent basis.
This “big picture” approach allows security decision-makers to prioritize the most critical exposures based on their actual potential impact in an attack scenario. It saves valuable time and resources by allowing teams to focus only on exposures that could be useful to attackers. And, it continuously monitors for new threats and reevaluates overall risk across the environment.
By helping organizations focus on what truly matters, Exposure Management empowers them to more efficiently allocate resources and demonstrably improve overall cybersecurity posture.
Now let’s look at the other common approaches used to understand and address exposures and see how they stack up against, and compliment Exposure Management.
Exposure Management vs. Penetration Testing (Pentesting)
Penetration Testing (Pentesting) simulates real-world attacks, exposing vulnerabilities in an organization’s defenses. In Pentesting, ethical hackers mimic malicious actors, attempting to exploit weaknesses in applications, networks, platforms, and systems. Their goal is to gain unauthorized access, disrupt operations, or steal sensitive data. This proactive approach helps identify and address security issues before they can be used by real attackers.
While Pentesting focuses on specific areas, Exposure Management takes a broader view. Pentesting focuses on specific targets with simulated attacks, while Exposure Management scans the entire digital landscape using a wider range of tools and simulations.
Combining Pentesting with Exposure Management ensures resources are directed toward the most critical risks, preventing efforts wasted on patching vulnerabilities with low exploitability. By working together, Exposure Management and Pentesting provide a comprehensive understanding of an organization’s security posture, leading to a more robust defense.
Exposure Management vs. Red Teaming
Red Teaming simulates full-blown cyberattacks. Unlike Pentesting, which focuses on specific vulnerabilities, red teams act like attackers, employing advanced techniques like social engineering and zero-day exploits to achieve specific goals, such as accessing critical assets. Their objective is to exploit weaknesses in an organization’s security posture and expose blind spots in defenses.
The difference between Red Teaming and Exposure Management lies in Red Teaming’s adversarial approach. Exposure Management focuses on proactively identifying and prioritizing all potential security weaknesses, including vulnerabilities, misconfigurations, and human error. It utilizes automated tools and assessments to paint a broad picture of the attack surface. Red Teaming, on the other hand, takes a more aggressive stance, mimicking the tactics and mindset of real-world attackers. This adversarial approach provides insights into the effectiveness of existing Exposure Management strategies.
Red Teaming exercises reveal how well an organization can detect and respond to attackers. By bypassing or exploiting undetected weaknesses identified during the Exposure Management phase, red teams expose gaps in the security strategy. This allows for the identification of blind spots that might not have been discovered previously.
Exposure Management vs. Breach and Attack Simulation (BAS) Tools
Unlike traditional vulnerability scanners, BAS tools simulate real-world attack scenarios, actively challenging an organization’s security posture. Some BAS tools focus on exploiting existing vulnerabilities, while others assess the effectiveness of implemented security controls. While similar to Pentesting and Red Teaming in that they simulate attacks, BAS tools offer a continuous and automated approach.
BAS differs from Exposure Management in its scope. Exposure Management takes a holistic view, identifying all potential security weaknesses, including misconfigurations and human error. BAS tools, on the other hand, focus specifically on testing security control effectiveness.
By combining BAS tools with the broader view of Exposure Management, organizations can achieve a more comprehensive understanding of their security posture and continuously improve defenses.
Exposure Management vs. Risk-Based Vulnerability Management (RBVM)
Risk-Based Vulnerability Management (RBVM) tackles the task of prioritizing vulnerabilities by analyzing them through the lens of risk. RBVM factors in asset criticality, threat intelligence, and exploitability to identify the CVEs that pose the greatest threat to an organization.
RBVM complements Exposure Management by identifying a wide range of security weaknesses, including vulnerabilities and human error. However, with a vast number of potential issues, prioritizing fixes can be challenging. Exposure Management provides a complete picture of all potential weaknesses, while RBVM prioritizes exposures based on threat context. This combined approach ensures that security teams are not overwhelmed by a never-ending list of vulnerabilities, but rather focus on patching the ones that could be most easily exploited and have the most significant consequences. Ultimately, this unified strategy strengthens an organization’s overall defense against cyber threats by addressing the weaknesses that attackers are most likely to target.
The Bottom Line#
At XM Cyber, we’ve been talking about the concept of Exposure Management for years, recognizing that a multi-layer approach is the very best way to continually reduce risk and improve posture. Combining Exposure Management with other approaches empowers security stakeholders to not only identify weaknesses but also understand their potential impact and prioritize remediation. Cybersecurity is a continuous battle. By continually learning and adapting your strategies accordingly, you can ensure your organization remains a step ahead of malicious actors.
Note: This expertly contributed article is written by Shay Siksik, VP Customer Experience at XM Cyber.





