A sophisticated Magecart campaign has been observed manipulating websites’ default 404 error page to conceal malicious code in what’s been described as the latest evolution of the attacks.
The activity, per Akamai, targets Magento and WooCommerce websites, with some of the victims belonging to large organizations in the food and retail industries.
“In this campaign, all the victim websites we detected were directly exploited, as the malicious code snippet was injected into one of their first-party resources,” Akamai security researcher Roman Lvovsky said in a Monday analysis.
This involves inserting the code directly into the HTML pages or within one of the first-party scripts that were loaded as part of the website.
The attacks are realized through a multi-stage chain, in which the loader code retrieves the main payload during runtime in order to capture the sensitive information entered by visitors on checkout pages and exfiltrate it to a remote server.
“The purpose of separating the attack into three parts is to conceal the attack in a way that makes it more challenging to detect,” Lvovsky explained. “This makes the attack more discreet and more difficult to detect by security services and external scanning tools that might be in place on the targeted website.”
“This allows for the activation of the full flow of the attack only on the specifically targeted pages; that is, because of the obfuscation measures used by the attacker, the activation of the full attack flow can only occur where the attacker intended for it to execute.”
The use of 404 error pages is one of the three variations of the campaign, the other two of which obfuscate the skimmer code in a malformed HTML image tag’s onerror attribute and as an inline script that masquerades as the Meta Pixel code snippet.
The fake Meta Pixel code, for its part, fetches a PNG image from the website’s own directory that contains a Base64-encoded string appended to the end of the image binary file, which, when decoded, represents a piece of JavaScript code that reaches out to an actor-controlled domain to retrieve the second stage payload.
“This code is responsible for carrying out various malicious activities on the targeted sensitive page, with the goals of reading the user’s sensitive personal and credit card data and transmitting it back to the skimmer’s C2 server,” Lvovsky said.
Both these techniques are designed to circumvent security measures such as static analysis and external scanning, effectively prolonging the lifespan of the attack chain.
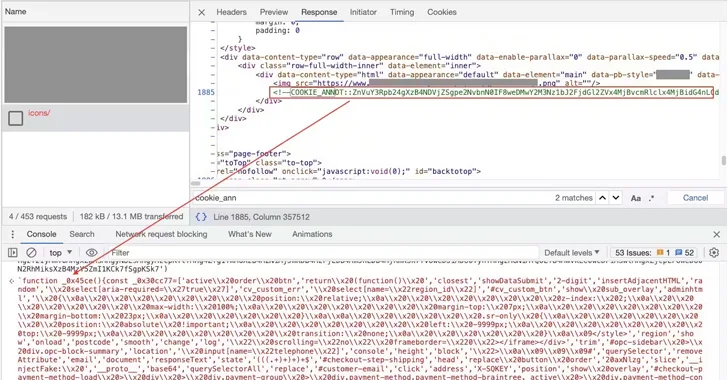
However, it’s the third loader variant that stands out for its unusual concealment technique by taking advantage of default error pages on the website. Appearing either as an inline script or a bogus Meta Pixel code, it sends a GET request to a non-existent URL in the website, triggering a “404 Not Found” response.
This response points to a modified error page hiding the skimmer code within it. The skimmer works by overlaying a lookalike payment form on checkout pages to capture the data for subsequent exfiltration in the form of a Base64-encoded string.
“The idea of manipulating the default 404 error page of a targeted website can offer Magecart actors various creative options for improved hiding and evasion,” Lvovsky said.
“The request to the first-party path leading to the 404 page is another evasion technique that can bypass Content Security Policy headers and other security measures that may be actively analyzing network requests on the page.”







