From a user’s perspective, OAuth works like magic. In just a few keystrokes, you can whisk through the account creation process and gain immediate access to whatever new app or integration you’re seeking. Unfortunately, few users understand the implications of the permissions they allow when they create a new OAuth grant, making it easy for malicious actors to manipulate employees into giving away unintended access to corporate environments. In one of the highest-profile examples, Pawn Storm’s attacks against the Democratic National Convention and others leveraged OAuth to target victims through social engineering.
Security and IT teams would be wise to establish a practice of reviewing new and existing OAuth grants programmatically to catch risky activity or overly-permissive scopes. And, there are new solutions for SaaS security cropping up that can make this process easier.
Let’s take a look at some best practices for prioritizing and investigating your organization’s grants.
When should you investigate an OAuth grant?
Organizations approach OAuth grant reviews in a few different ways. Some opt to review new OAuth grants in real-time, initiating a review any time a user signs up for a new application or connects an integration. An even better practice would be to tailor your Google or Microsoft settings to require administrative approval for any new grant before employees can start using it, giving your team time to investigate and catch anything suspicious.
While reviewing new OAuth grants can help you detect issues early on, oversight shouldn’t end once an OAuth grant is in place. It’s important to maintain OAuth security hygiene by reviewing grants on an ongoing basis to detect high-risk activity or drastic changes. Monthly or quarterly, security and IT teams should audit existing OAuth grants, check for changes, and prune the grants that haven’t been used.
Tailor your investigations by assessing OAuth scopes.
OAuth authentication works by assigning access tokens to third-party applications that can act as a proxy for a user’s consent, and the scope of permissions granted can range broadly. You can prioritize your OAuth investigations by considering the scope of access each grant provides.
Because different scopes carry different levels of risk to your organization, you can vary the standards of your investigations based on the permissions granted. Focus more attention on grants with scopes that are more likely to give access to critical information, such as personally identifiable information (PII) or intellectual property, or grants that can make changes to an application.
And, you may want to look into tools that can assemble an inventory of all OAuth grants for you, along with scopes and OAuth risk scores to make this process easier.
Evaluate OAuth vendors and their reputations.
Assess whether or not the vendor responsible for issuing the OAuth grant is trustworthy. For example, you can review the vendor’s security page, look at their security certifications, and make sure their security program follows best practices.
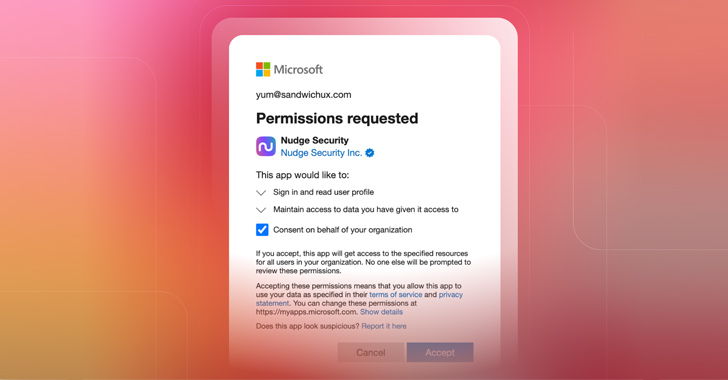
Certain reputational signals can help you understand the level of trust other organizations have placed in the grant. For example, Microsoft and Google both have systems for verifying the identity of app publishers, which can give you more confidence in the grant. However, attackers have managed to exploit verified publisher statuses in recent attacks, so practitioners should consider them a helpful signal rather than a definitive assessment of an app’s trustworthiness.
The popularity of a particular application, and of a particular grant, can provide yet another trust indicator. If the grant isn’t new to your organization, you can consider its popularity within your own workforce by taking a look at how many of your own employees are using it and with what frequency. You can even extend this to the popularity or number of installs outside of your organization in the case that the OAuth application is present in the Google marketplace.
Check the OAuth grant’s domains.
Before you can rely on a brand’s reputation, you need to make sure that the grants listed actually belong to the vendor you’re trying to verify. Checking a grant’s domains can help you determine whether a vendor actually backs that particular OAuth grant, or if the grant was created by someone trying to piggyback off of a legitimate brand’s reputation.
For example, if the grant’s reply URL is calendly3.com, you should make sure it’s actually a Calendly domain and not a malicious copycat. You should investigate whether the name of the grant matches the URL, and whether the domain has been approved by Google.
Investigate the publisher email.
You can gain additional insight into a grant’s legitimacy by looking into the publisher email, which is the email address used to register the client ID used by the OAuth token.
Sometimes, an OAuth grant publisher will use a personal email address from a freemail provider like Gmail, which may indicate some risk. If that’s the case, you can look into the reputation of that email to understand the likelihood that it may have been used for malicious intent. For example, make sure there are no compromised credentials floating around that could enable a bad actor to take over the email account. Microsoft recently warned of threat actors exploiting stolen Exchange Online accounts to spread spam using malicious OAuth applications. The actors gained initial access to the stolen accounts using credential stuffing attacks, which means compromised credentials would have been an early indicator of risk.
Evaluate how the vendor is accessing your environment.
Keeping an eye on how a vendor accesses your environment can help you flag sudden changes and identify suspicious activity. For example, let’s say you allow an OAuth grant to access your organization’s email. For three months, they access it by calling Google Workspace APIs from Amazon AWS. Suddenly, you get a high-risk API call from a completely different infrastructure (TOR exit node, proxy network, VPS, etc). Perhaps the vendor has been compromised, or maybe the application’s credentials have been stolen. If you’re monitoring activity related to how these vendors are accessing your environment, this type of change can indicate a potential problem.
Your organization’s ability to monitor this activity may depend on the level of service you pay for. For example, Google requires a special license to access an activity stream that reveals what APIs are called within your environment, as well as when and how they’re accessed. If you don’t pay for the activity stream and an incident occurs, you may be blind.
Microsoft, on the other hand, recently changed their stance on log access by opting to make cloud logs available to all users rather than only premium license holders. The change followed pressure from CISA and others after government email accounts at multiple agencies were hacked, which would not have been discoverable without premium logging available to at least one of the affected parties.
Monitor the security posture of your OAuth vendors.
As part of your ongoing monitoring, keep an eye out for high-profile supply chain attacks that may have affected your OAuth vendors. If a provider in your vendor’s supply chain experiences a data breach, could it compromise your own security posture?
Similarly, consider the effect of major vulnerabilities on the vendors you rely on. When a widely exploited vulnerability like the ones found in Apache Log4j becomes public, assess whether any of the vendors with OAuth access to your environment might be affected. Similarly, you should pay attention to vulnerabilities within OAuth grants themselves, like the Microsoft “nOAuth” misconfiguration that can enable bad actors to take over affected accounts. If you believe your vendors may be affected, you may choose to take an action like revoking those grants until you know that the vulnerability has been resolved.
Investigate and revoke high-risk OAuth grants with Nudge Security.
Nudge Security is a SaaS management platform for modern IT governance and security. It provides complete visibility of every SaaS and cloud asset ever created by anyone in your org, including OAuth grants. The platform provides an inventory of every app-to-app OAuth grant ever created in your org, along with OAuth risk insights like grant type, age, number of scopes, who granted access, and an overall OAuth risk score. With this visibility, users can easily conduct OAuth reviews, assess risk, and even revoke OAuth grants with just two clicks. Try it for free.
Note: This article was expertly written and contributed by Jaime Blasco, CTO and co-founder of Nudge Security.








